[This post is part of WordPress Security series.]
As WordPress grows popular, more people begin to use it for their websites, right? Over 23% of all websites or 74.6+ million websites are powered by WordPress software. What does that mean? That purely means that if WordPress' one vulnerability is discovered, millions of sites are at stake! That's terrifying, right?
If you want to stop hackers from hacking your site, you must first understand how do they compromise your site. That's how you stop hackers. So how do hackers do it? First, there's not one way to do it. There are many different ways they can break into a site.

Unreliable Web Host
There are hundreds of web hosts out there, all competing with each other, claiming to be reliable, safe, etc. But not all web hosts are safe and it is of very importance to choose a web host that is both reliable and safe.
According to a survey by WP White Security, 41% of all hacked WordPress sites were hacked due to vulnerabilities in their web hosting platform. This clearly expresses a need for guidance regarding choosing reliable web hosts.
Nulled Plugins and Themes
Before plugins and/or themes are hosted at WordPress repositories, they are reviewed by professionals for vulnerabilities. This is a precaution in case someone tries to upload malicious plugin or theme. Though not plugins and themes from official directory are pure of vulnerabilities, but most are reliable.
Which is why you should always download themes and plugins from WordPress repositories. You should never download themes or plugins from unofficial sources, especially plugins/themes which are supposed premium. Because typically, they contain malicious scripts allowing hackers exploit your site. 51% of sites were hacked due to this one mistake!
Weak Passwords
8% of sites got hacked due to weak passwords. Passwords like "123456", "password12345" and "password" are too common to be used to protect your precious site, no? Hackers use automated scripts that try to guess passwords all the time, don't make it so easy for them! By the way, this way of breaking in to a site is called Brute Force.
Always try to complicate your password by adding capitals, numerals, punctuations, etc. Or you can use password generators like LastPass Generate Password, Strong Random Password Generator and Norton Password Generator.
Default Admin Username
Years back, WordPress would set admin as administrator's username by default. Fast forward years later, though WordPress now allows changing username, but it has kind of become standard and hackers know this.
So people still choose this, compromising their site's security unknowingly. Hackers know that admin used to be the default administrator username, so they Brute Force against admin username.
If you're using admin as the username, do change it! To change it easily, simply use Admin renamer extended plugin.
Un-updated Version of WordPress
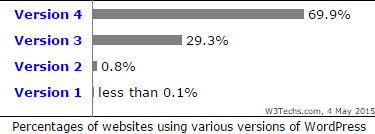
This is among the most common causes of WordPress getting hacked. WordPress releases major updates every few weeks and minor security fixes are always coming out. Your site is more likely to be affected by attacks if you're using an older version. In 3.7, WordPress released a feature that would automatically update WordPress to the latest version. But by default, this feature only automated minor updates, not major ones. Major updates are typically more likely to break site, so they should be updated manually so if site breaks, you can deactivate uncompatible plugins and fix it.
If you're unable to update WordPress manually and don't like the idea of automation, you can hide your current version (so hackers won't know if you're on an older version). To hide version, use Remove Version plugin.
Still if you want to automate major updates as well as minor ones, add following line to your wp-config.php file:
define( 'WP_AUTO_UPDATE_CORE', true ); // automates all updates
Weak File Permissions
On computers, files and directories have certain permissions. These permissions define who can and cannot read, write and execute these files. WordPress requires certain permissions for wp-content directory to execute functions.
There are 3 groups of people with different permissions; the user, the file group and everyone else. Any group with too permissions can read, modify and execute files. This is why you want to only give as many permissions as needed, no more or less.
Default Table Prefix
You also have a database to secure. By default WordPress applies table prefix 'wp_' to all tables created by said software. Since hackers know this, they can use this information to do SQL injection. If you change this table prefix to something different, you make hackers guess table prefix. So that makes you less susceptible to SQL injection vulnerabilities.
Exploiting Critical Files
There are certain files among WordPress core files that are more important than other. Because they affect every other file. wp-config.php is configuration file, which establishes database connection and does a lot of things. .htaccess is a server configuration file, which operates server. These files can give away as well as secure keys to your site.
If only any one of these files are compromised, no matter how secure your rest of the installation is, hacker won already! So it should be your top priority to keep files away from hacker's access.
Conclusion
Aside from aforementioned ways, there are many other ways a hacker can do his thing. But fixing these security holes should suffice. We will be talking about each security technique in details in upcoming posts.
[This post is part of WordPress Security series.]
